AI Security

Directing AI
Virtualization & Alternatives

Marquee Account Planning
Presentation by Mark Campbell about the best methodologies for streamlining and maximizing the impact of executive meetings
EU: Executive Presentations, Myth & Truth

Presentation by Mark Campbell about the best methodologies for streamlining and maximizing the impact of executive meetings
Q4 Lab Results: Play of the Quarter AI Roadmap

Looking Back, Looking Forward
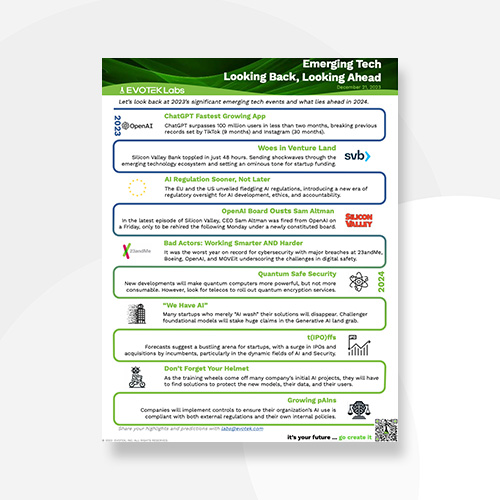
As we wrap up an eventful year, it’s time to reflect on the significant strides in emerging tech during 2023 and set our sights on what’s ahead in 2024.
Our latest December Lab Report is a deep dive into the year’s major tech breakthroughs and a sneak peek at the trends shaping the upcoming year.
Within EVOTEK Labs’ insightful reports, we uncover pivotal moments, innovative solutions, and impactful results within the realm of emerging tech. Keep an eye out for our next report—it’s your guide to staying at the forefront of innovation!
Vulnerability Management

Cloud costs are unpredictable, lack transparency, siloed across teams, and are inefficiently managed, leading to wasted spending and misalignment with business priorities.
Posture Management

Cloud costs are unpredictable, lack transparency, siloed across teams, and are inefficiently managed, leading to wasted spending and misalignment with business priorities.
Q3 Lab Results: AI Risk Assessments